Total Security Management: A Comprehensive Guide to Enhancing Security Posture

In today's increasingly interconnected and complex world, organizations face a myriad of security threats that can jeopardize their operations, reputation, and financial stability. To effectively address these challenges, a comprehensive and integrated approach to security management is essential. Total Security Management (TSM) provides a holistic framework that encompasses all aspects of security, enabling organizations to establish a robust and resilient security posture.
4.5 out of 5
| Language | : | English |
| File size | : | 3479 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Word Wise | : | Enabled |
| Print length | : | 312 pages |
What is Total Security Management?
Total Security Management is a comprehensive approach that integrates physical security, cybersecurity, risk management, and audit compliance into a unified framework. It recognizes that security is not a static state but an ongoing process that requires continuous monitoring, assessment, and improvement.
TSM is based on the principle of defense-in-depth, which involves implementing multiple layers of security controls to protect assets and information. These controls can include physical barriers, access controls, intrusion detection systems, and firewalls. By combining physical and cybersecurity measures, organizations can create a more robust security posture that is less vulnerable to attack.
Benefits of Total Security Management
Implementing a Total Security Management approach offers numerous benefits to organizations, including:
*
- Enhanced Security: TSM provides a comprehensive and integrated approach to security, addressing all aspects of risk from physical threats to cyberattacks.
- Reduced Costs: By implementing a unified security framework, organizations can avoid duplicating efforts and reduce overall security costs.
- Improved Compliance: TSM helps organizations meet regulatory and industry security standards, reducing the risk of fines and penalties.
- Increased Efficiency: By streamlining security processes and automating tasks, TSM can improve operational efficiency and reduce administrative burdens.
- Enhanced Business Resilience: A robust security posture enables organizations to withstand and recover from security incidents, minimizing disruption to operations and revenue loss.
Key Components of Total Security Management
TSM encompasses a range of interconnected components that work together to provide a comprehensive security solution. These components include:
Physical Security
- Access control systems (e.g., key cards, biometrics)
- Physical barriers (e.g., gates, fences, security guards)
- Surveillance systems (e.g., CCTV cameras, motion sensors)
- Environmental controls (e.g., temperature and humidity monitoring)
- Disaster recovery and business continuity plans
Cybersecurity
- Network security (e.g., firewalls, intrusion detection systems)
- Endpoint security (e.g., antivirus software, patch management)
- Data security (e.g., encryption, access controls)
- Incident response and recovery plans
- Cybersecurity awareness and training
Risk Management
- Risk assessment and identification
- Risk analysis and prioritization
- Risk mitigation and control implementation
- Risk monitoring and reporting
- Risk management framework alignment (e.g., ISO 27001, NIST Cybersecurity Framework)
Audit Compliance
- Internal audits and compliance assessments
- Third-party audits and certifications (e.g., ISO 27001, SOC 2)
- Compliance with regulatory requirements (e.g., GDPR, HIPAA)
- Regular reporting and oversight
- Continuous improvement and remediation
Implementing Total Security Management
Implementing a Total Security Management approach requires a systematic and structured approach that involves the following steps:
1. Establish a Security Vision and Objectives
Define the organization's security goals and objectives, including the desired level of security and risk tolerance.
2. Conduct a Risk Assessment
Identify and assess the potential security risks the organization faces, considering both physical and cybersecurity threats.
3. Develop a Security Plan
Create a comprehensive security plan that outlines the specific measures and controls to be implemented to mitigate identified risks.
4. Implement Security Controls
Deploy the necessary physical, cybersecurity, risk management, and audit compliance controls according to the security plan.
5. Monitor and Maintain Security
Continuously monitor security systems and controls, and perform regular maintenance and updates to ensure ongoing effectiveness.
6. Audit and Review Security
Conduct regular audits and reviews to assess the effectiveness of implemented controls and identify areas for improvement.
Total Security Management is a comprehensive and integrated approach to security that enables organizations to establish a robust and resilient security posture. By addressing all aspects of security, from physical threats to cybersecurity risks, TSM helps organizations minimize their exposure to security incidents, maintain compliance, and protect their business reputation and financial stability. Implementing a TSM approach requires a commitment to continuous improvement and collaboration among all stakeholders, but it ultimately provides organizations with the foundation necessary to navigate the evolving security landscape and achieve their business objectives.
4.5 out of 5
| Language | : | English |
| File size | : | 3479 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Word Wise | : | Enabled |
| Print length | : | 312 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Chapter
Chapter Story
Story Genre
Genre Library
Library E-book
E-book Paragraph
Paragraph Bookmark
Bookmark Glossary
Glossary Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Scroll
Scroll Tome
Tome Bestseller
Bestseller Classics
Classics Reference
Reference Dictionary
Dictionary Thesaurus
Thesaurus Character
Character Librarian
Librarian Catalog
Catalog Card Catalog
Card Catalog Borrowing
Borrowing Archives
Archives Periodicals
Periodicals Reserve
Reserve Journals
Journals Reading Room
Reading Room Rare Books
Rare Books Special Collections
Special Collections Interlibrary
Interlibrary Study Group
Study Group Thesis
Thesis Storytelling
Storytelling Book Club
Book Club Textbooks
Textbooks Autumn Dawn
Autumn Dawn Sophie De Mullenheim
Sophie De Mullenheim Michelle Landon
Michelle Landon Siri Pettersen
Siri Pettersen Mark Lowery
Mark Lowery Jacques Chaize
Jacques Chaize Sanjeev Agarwal
Sanjeev Agarwal Terry Ambrose
Terry Ambrose Songy Knox
Songy Knox R Zamora Linmark
R Zamora Linmark Jennifer Brody
Jennifer Brody Brett Novick
Brett Novick Conor Kostick
Conor Kostick Tom Swyers
Tom Swyers Clint Arthur
Clint Arthur David Malet
David Malet Diane Pecknold
Diane Pecknold Rebecca Zeus
Rebecca Zeus Stephen Ducke
Stephen Ducke Jeevani Charika
Jeevani Charika
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Donovan CarterWhy Women in Leadership Create a Better World: Exploring the Multitude of...
Donovan CarterWhy Women in Leadership Create a Better World: Exploring the Multitude of... Ernest ClineFollow ·17.1k
Ernest ClineFollow ·17.1k August HayesFollow ·14.7k
August HayesFollow ·14.7k Frank MitchellFollow ·19.8k
Frank MitchellFollow ·19.8k John Dos PassosFollow ·13.5k
John Dos PassosFollow ·13.5k Felix CarterFollow ·13.5k
Felix CarterFollow ·13.5k Julio Ramón RibeyroFollow ·19.1k
Julio Ramón RibeyroFollow ·19.1k William FaulknerFollow ·5.2k
William FaulknerFollow ·5.2k Patrick RothfussFollow ·10.1k
Patrick RothfussFollow ·10.1k
 Dylan Hayes
Dylan HayesUnscientific America: 11. Harris and Chomsky
In this chapter...
 Kenneth Parker
Kenneth ParkerThe Ultimate Flight Attendant Essential Guide: A...
If you're passionate about travel, meeting...
 Bill Grant
Bill GrantFrom Armed Struggle to Political Struggle: The Evolution...
Liberation movements have...
 Brady Mitchell
Brady MitchellSquirreled Away: Boy Meets Squirrels, Nutty Study...
In the heart of a sprawling...
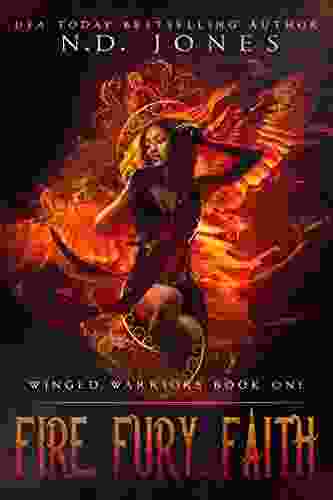
 Pete Blair
Pete BlairFire Fury Faith: An Angel Romance with Winged Warriors
Synopsis Fire Fury...
4.5 out of 5
| Language | : | English |
| File size | : | 3479 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Word Wise | : | Enabled |
| Print length | : | 312 pages |